Hack.lu CTF 2014 - douchemac
For this challenge we have a PCAP network dump. After some initial analysis we recognized that it recorded some interaction with wildwildweb.fluxfingers.net on port 1420 using the DBus protocol.
Using python we can quite easily build a script that connects to the same service and interacts with it
import dbus
host = "tcp:host=wildwildweb.fluxfingers.net,port=1420"
bus = dbus.bus.BusConnection(host)
p = bus.get_object('test.test123.Server', '/Server')
server_iface=dbus.Interface(p, dbus_interface='test.test123.Server')
print server_iface.dbus_start()
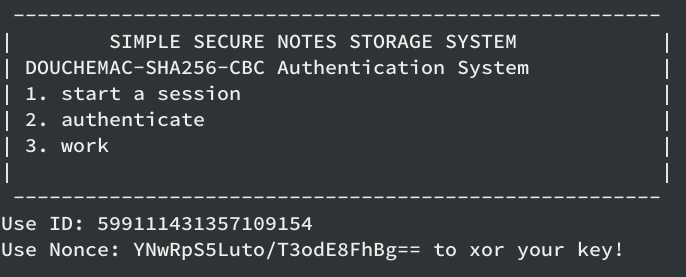
…and we got the same message as in the network dump:
From the network dump and the dbus interface we know that we can use the following methods:
- dbus_genrnd(id)
- dbus_authc(id, msg, iv, tag)
- dbus_auths(id, msg)
- dbus_time(id)
- dbus_list(id)
- dbus_put(id, filename, text)
- dbus_get(id, filename)
- dbus_start()
Unfortunately only some can be used without authentication :( so let’s try to authenticate:
- With dbus_auths(id, msg) we can send a message (base64 encoded) and get it signed. We get back the base64 encoding of the IV and the tag (i.e.: the signature).
- We need to send back any message with a valid tag and IV, but we don’t know much about how the signature is produced. Furthermore there are some restrictions:
- We cannot send back the same signed message we received, the service returns “Authentication: 0”
- The message not only needs to be different, it also needs to be of a different block length
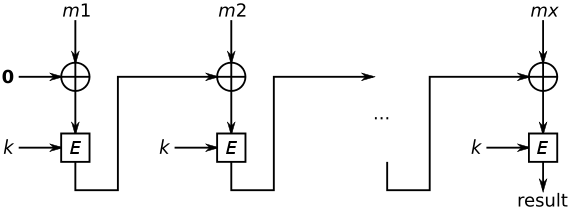
Let’s look at Wikipedia, how CBC-MAC works:
My first try was to get a first message signed, then set the message to (first_message xor IV) and IV to all zeros: in this way we have a different message with the same valid signature that we previously obtained. However the second restriction does not allow it.
Luckily we can use a similar approach to get a different and longer message with the same signature of the initial one:
M = initial_msg || (initial_msg xor IV xor tag)
In this way at the second step of the chain we end up with:
E(tag xor (initial_msg xor IV xor tag)) = E(initial_msg xor IV) = tag
After the authentication process we can just request the list of files and get secret.txt that contains the flag. This script automates it all.