| categories:writeups series:Flare-On Challenges 2015
Flare-On Challenges 2015 - #7 YUSoMeta
I would like to post a brief writeup for Flare-On challenge #7. There are other very comprehensive solutions but, as mine is different and simpler, I think it’s still interesting to show.
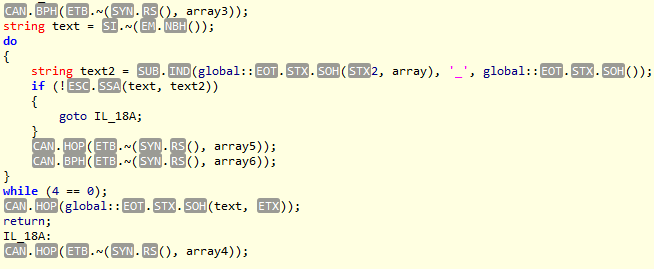
First I used ILSpy to get a decompilation of the .NET executable. After few minutes I noticed this part of the code
where text is the correct input while text2 is the user input.
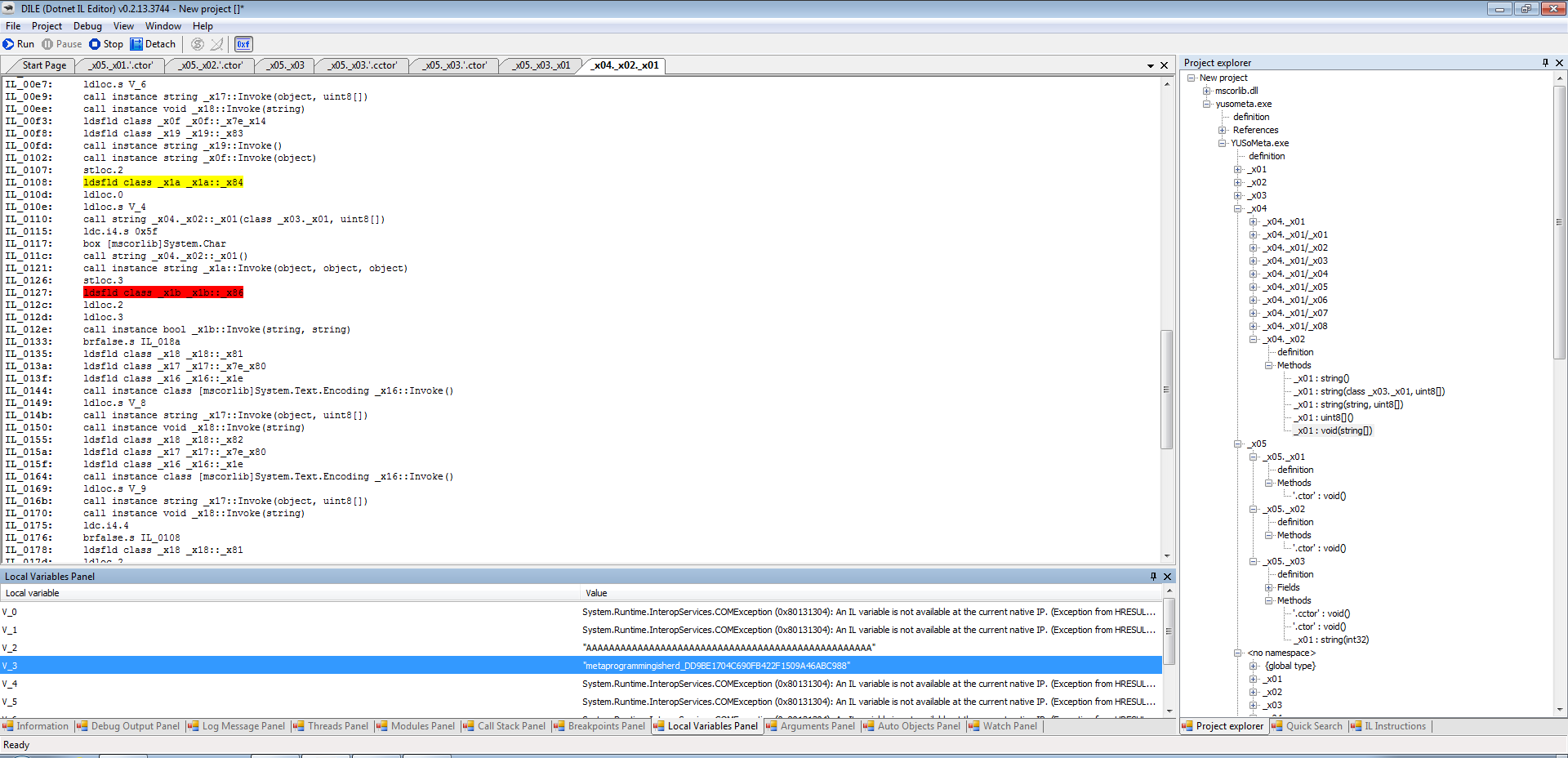
So I fired DILE and tried to get debugging. The steps I did are the following:
- Match the IR in DILE with the decompiled code in ILSpy in order to find the target method. I knew that the method I was looking for was accepting a
string[]as argument so I searched for such methods. I ended up finding\x04.\x02.\x01. - Find a spot where to set a breakpoint. Any place after the
textvariable was populated was fine. I set a breakpoint atIL_127. - Launch YUSoMeta.exe
- Attach DILE to the process
- Enter a random string in the binary
- Hit the breakpoint in DILE, move to the “Local variables Panel” and get the key: “metaprogrammingisherd_DD9BE1704C690FB422F1509A46ABC988”